Debugging in prod: Maximizing user attack surface
Note: This is a super quick write-up and probably still full of typos and stylistic errors, which you’re free to point out in the comment section.
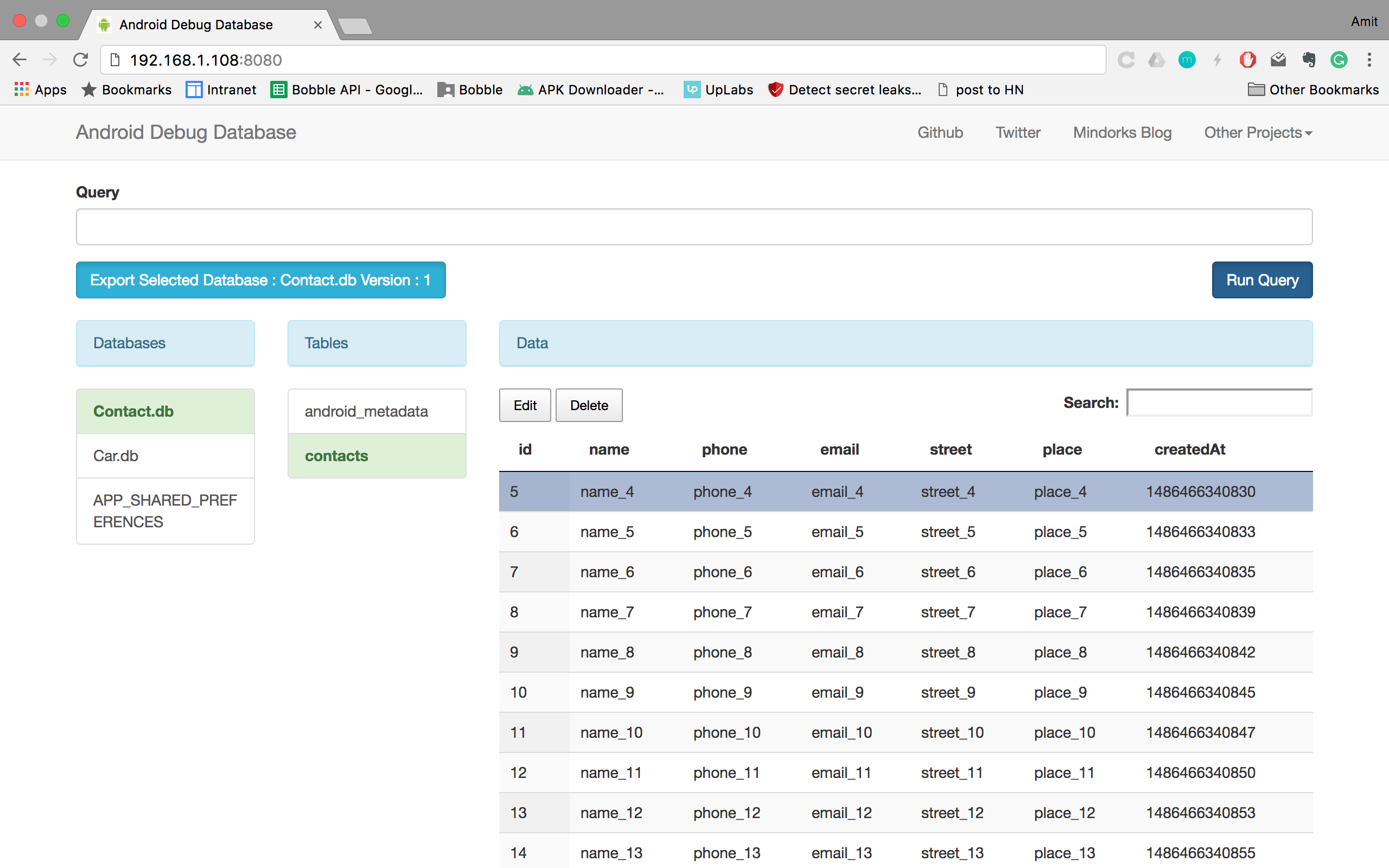
One thing that’s really cool about the Android developer ecosystem, is the massive amount of tools and libraries to simplify and help during development. There is an entire subgenre of various remote debugging tools, with cool tools such as Stetho or Debug Drawer. One such tool is Android-Debug-Database from Mindorks, it’s a neat little utility that allows you to view and edit your apps preferences and dbs from a web browser during development.
The key phrase here is, of course, in development, which makes sense to everyone (and is also explained in the integration guide of the library), right? Well, no. During todays Shodan safari I randomly stumbled into a phone running this, openly available for anyone to play around with (Brazilian ISPs having all ports open per default be thanked). On closer inspection it turns out there are thousands of devices indexed on Shodan running debug db.
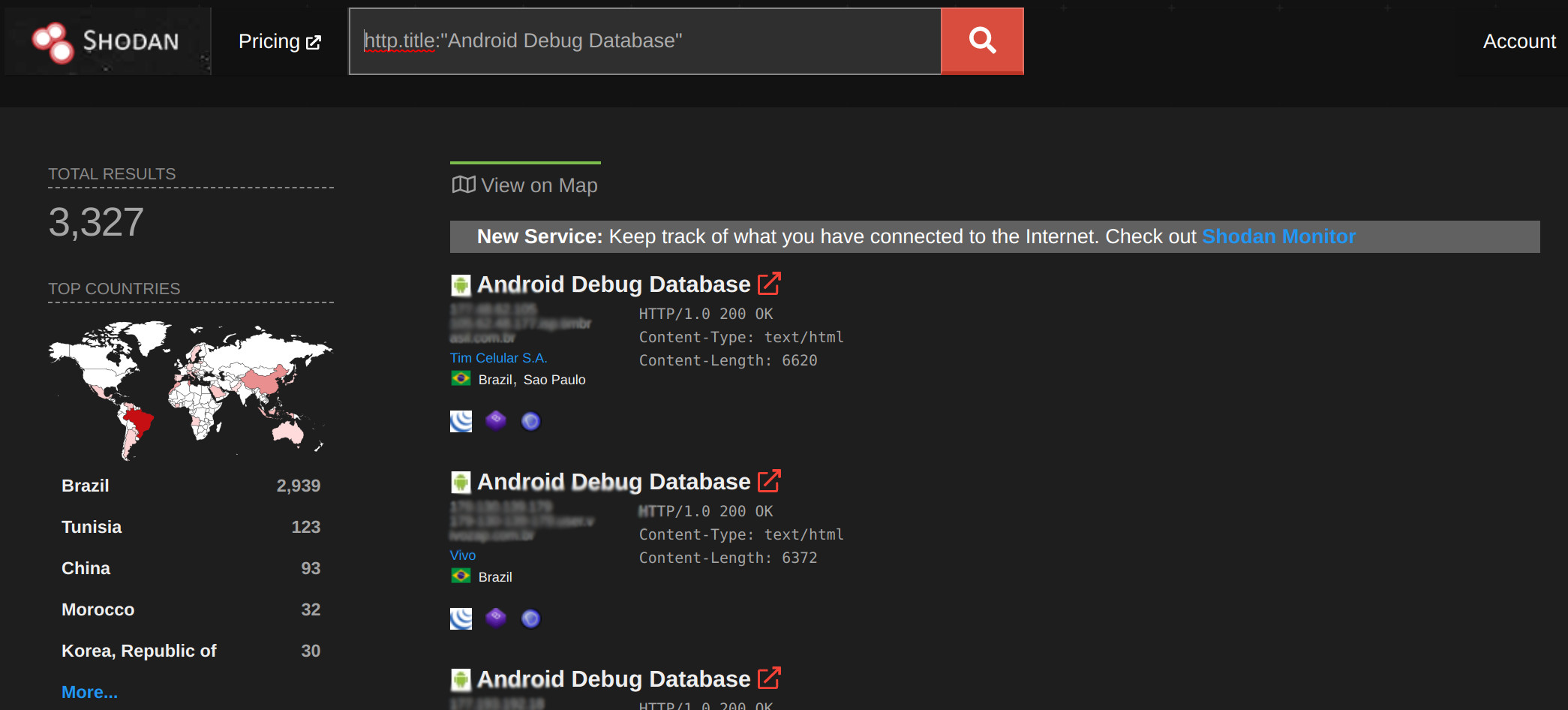
I took a look at some of these to figure out some notable apps, here are two of them:
Cinemark Brazil - 1M+ downloads
No Last Seen for WhatsApp - 50K+ downloads (yes, this allows reading all contacts and messages in the db)
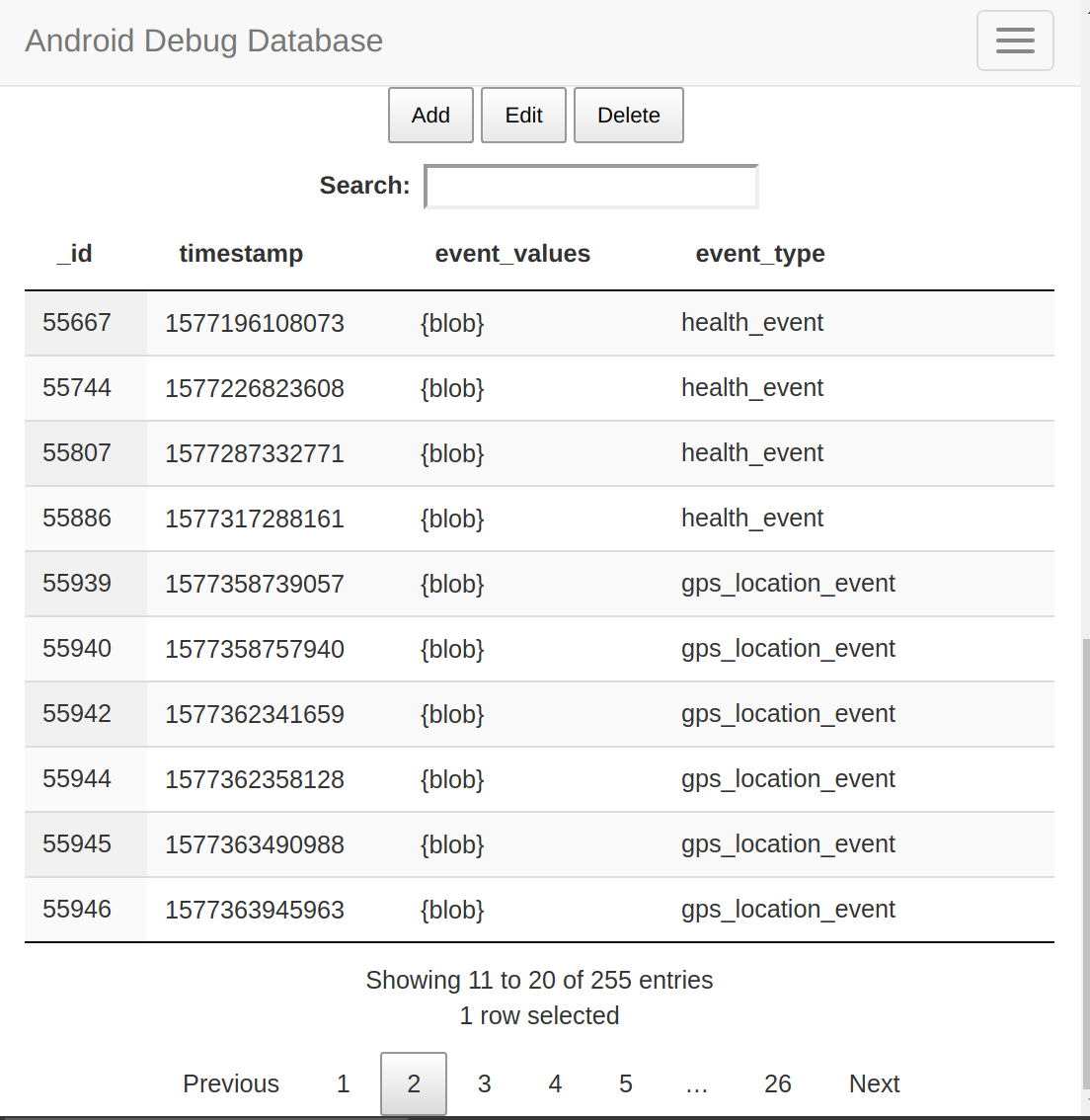
Some of these apps include logs of sensor and location data.
I downloaded Cinemark to verify this for myself, and I was indeed able to read and edit the app’s db and prefs by opening the app and going to localhost:8080. This is especially ironic considering the app also uses the ThreatMetrix sdk, which is some Enterprise Risk management (read: corporate spyware) sdk which supposedly also prevents cybersecurity threats.
The damning thing here is that we have to consider that most ISPs won’t allow access to their clients on port 8080 (at least not without UpNp), but this will always work inside networks, thus opening up another huge security threat with public WiFis. This also makes me wonder how many other apps are out there, shipping this to all their users and opening them up for attacks by literally anyone. Another terrible thing is that this library allows editing of the data in the db and the prefs, so the actual possible ways to exploit this outside data exfiltration reach far as well.